Search News
Industry Portal
Popular Tags
Automation Technology for Factories: Key Risks

Author
Time
Click Count
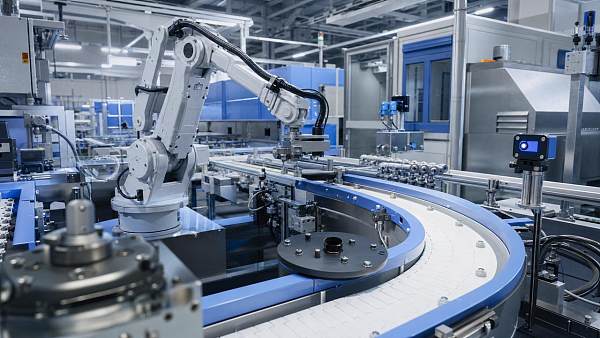
As manufacturers accelerate digital transformation, automation technology for factories is becoming essential to productivity, precision, and scalability. Yet for business evaluators, the real challenge lies in identifying the hidden risks behind adoption—from integration complexity and cybersecurity exposure to supplier dependency and compliance pressure. Understanding these factors is critical to making resilient, future-ready investment decisions.
For most buyers, the core question is not whether factory automation creates value. It is whether the proposed system can deliver measurable gains without introducing operational, financial, or strategic risk.
That is the real search intent behind automation technology for factories in a business evaluation context. Decision-makers want a practical framework for judging risk, vendor credibility, implementation feasibility, and long-term return.
They are not looking for a generic overview of robots, sensors, and software. They need to know what can go wrong, how often it happens, and how to assess exposure before capital is committed.
Business evaluators usually care most about five issues: integration difficulty, downtime risk, cybersecurity, total cost of ownership, and supplier lock-in. Compliance, workforce readiness, and scalability also matter because they affect payback and resilience.
This article focuses on those decision-critical areas. Rather than treating every automation topic equally, it concentrates on the risks that most directly influence investment quality and factory performance over time.
Why risk assessment matters more than feature comparison

In many automation projects, feature lists look impressive. Vendors emphasize machine vision accuracy, predictive maintenance dashboards, autonomous material handling, and AI-enabled control. These capabilities may be valuable, but they do not guarantee business success.
A strong evaluation starts with the factory’s operating reality. If a system cannot integrate with legacy equipment, support required production tolerances, or fit maintenance capacity, advanced features become secondary.
For business evaluators, the priority is exposure mapping. That means asking how automation technology for factories could affect throughput, quality, labor dependency, safety performance, and continuity under failure conditions.
The best investment decisions compare expected gains against downside scenarios. A system that promises high productivity but creates single points of failure may weaken the operation instead of strengthening it.
This is especially important in complex manufacturing environments where multiple assets, suppliers, and software layers interact. Risks often emerge not from one component, but from the connections between systems.
Integration risk is often the first hidden cost
Integration is one of the most underestimated risks in factory automation. Many projects fail to meet expected timelines because new platforms must connect with older PLCs, MES layers, ERP systems, and machine-specific protocols.
On paper, interoperability may appear manageable. In practice, data formats, communication standards, equipment age, and undocumented customizations can create extensive engineering work that was not fully priced at procurement stage.
For evaluators, this means the purchase price alone is not a reliable indicator of project cost. Integration engineering, middleware, testing, commissioning, and production interruptions can materially change the investment case.
A useful review question is whether the vendor has deployed similar systems in comparable factories. General technical competence is less important than proven success in environments with similar process complexity and asset diversity.
It is also wise to request a detailed integration architecture before approval. Evaluators should look for interface ownership, fallback procedures, data governance logic, and a realistic commissioning sequence.
If the vendor cannot clearly explain how the system will coexist with existing operations, risk is already visible. Ambiguity at the design phase often becomes delay, rework, and cost escalation later.
Downtime risk can erase automation ROI faster than expected
Automation is usually justified by efficiency gains, labor optimization, and output consistency. However, those gains can be quickly offset if the automated process becomes difficult to recover when something fails.
Manual systems may be less efficient, but they are sometimes more flexible under disruption. A highly automated line can be productive under normal conditions while being far more vulnerable during faults or software instability.
Business evaluators should examine mean time to repair, spare parts strategy, redundancy design, and remote support responsiveness. These factors influence actual uptime more than sales presentations typically suggest.
Another key issue is failure propagation. If one robot, controller, or sensor fault stops an entire line, the system may have poor operational resilience. Modular containment is often more valuable than peak theoretical speed.
Ask whether operators can run degraded modes safely when selected functions are unavailable. A factory that can sustain partial output during disruption is financially stronger than one that must halt completely.
Risk-adjusted ROI should therefore include not only productivity improvement, but also the economic impact of outages, troubleshooting delays, and dependence on specialist intervention.
Cybersecurity is no longer a side issue in industrial automation
As automation technology for factories becomes more connected, cybersecurity moves from IT concern to board-level operational risk. Industrial networks, remote diagnostics, cloud platforms, and edge devices all expand the attack surface.
For business evaluators, the key question is not simply whether a vendor claims secure architecture. It is whether security controls are appropriate for industrial uptime requirements, access management, and incident recovery.
Weak segmentation between operational technology and enterprise systems can allow disruptions to spread. Poor credential discipline, outdated firmware, and unmanaged remote access create especially serious exposure in manufacturing settings.
Cyber incidents in factories do not only threaten data. They can interrupt production, damage equipment, compromise safety, and trigger contractual or regulatory consequences. That makes cybersecurity central to investment evaluation.
Useful due diligence points include patch management responsibility, network segmentation design, encryption standards, log visibility, privileged access controls, and the vendor’s incident response process.
It is also important to review how the automation provider handles software updates over time. If long-term support is weak, the system may become an operational liability well before its physical components reach end of life.
Supplier dependency and lock-in can create long-term strategic risk
Many automation solutions are sold as integrated ecosystems. This can simplify deployment, but it may also create dependence on one supplier for software licenses, proprietary parts, support access, and future expansion.
In the short term, a bundled system may look efficient. Over several years, however, switching costs can rise sharply if interfaces are closed, documentation is limited, or only certified vendor personnel can perform critical changes.
For procurement and evaluation teams, this is not just a technical issue. Supplier lock-in affects negotiation leverage, lifecycle cost, upgrade flexibility, and continuity if the vendor changes direction or support quality declines.
To assess this risk, review licensing terms, data portability, source documentation depth, and third-party serviceability. Ask whether core components follow open standards or are intentionally optimized for ecosystem dependence.
Factories with global operations should also consider regional support coverage. A strong supplier in one geography may be inconsistent in another, which matters when standardization across sites is part of the automation strategy.
The safer path is not always avoiding integrated platforms. It is understanding where dependence is acceptable, where modularity is required, and how exit options will be preserved.
Total cost of ownership is broader than capital expenditure
Automation investment decisions often focus too heavily on upfront equipment cost. For business evaluators, a better metric is total cost of ownership across deployment, operations, upgrades, support, and eventual reconfiguration.
Software subscriptions, specialist maintenance, calibration, training, validation, cybersecurity upgrades, and spare inventory all influence the real economics. These recurring costs are frequently understated during initial vendor conversations.
Energy use can also become significant, especially in high-throughput operations with continuous robotic activity, compressed air demand, thermal control, or edge computing loads. Sustainability-linked reporting may elevate this issue further.
Another cost driver is change management. If every process modification requires external engineering support, the factory may face both direct cost and slower response to market shifts.
Evaluators should model at least three scenarios: expected case, delayed deployment case, and underperformance case. This approach produces a more realistic view of payback sensitivity and downside tolerance.
When automation technology for factories is assessed through lifecycle economics instead of purchase price, weak business cases become easier to identify before contracts are signed.
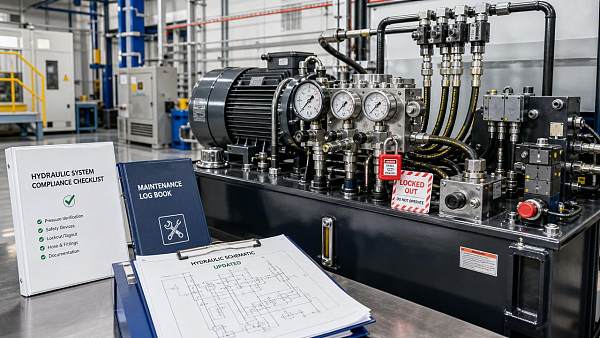
Compliance, safety, and data governance should be addressed early
In regulated or high-liability manufacturing environments, compliance risk can materially affect automation decisions. Safety validation, traceability requirements, quality records, and data retention obligations must align with system design.
If these requirements are treated as post-purchase adjustments, implementation becomes slower and more expensive. In some cases, retrofitting compliance features can undermine the original economic rationale.
Business evaluators should ask whether the automation solution supports auditability, event logging, access records, and process traceability at the level required by the operation and customer contracts.
Safety is equally important. Automated systems can reduce human exposure to hazardous tasks, but they also introduce motion, control, and interaction risks that require rigorous engineering and governance.
Data governance deserves more attention as well. When production data flows across machines, cloud platforms, analytics tools, and external vendors, ownership and access boundaries must be clearly defined.
A mature vendor should be able to explain not only system capability, but also how compliance, safety, and data responsibilities will be managed throughout the asset lifecycle.
Workforce readiness can determine whether the system performs as promised
Even advanced automation depends on people. Operators, maintenance teams, engineers, supervisors, and planners all influence whether the system delivers stable value after go-live.
One common risk is assuming the new technology will reduce labor complexity immediately. In reality, many factories face a transition period where skill requirements increase before efficiencies are fully realized.
If troubleshooting expertise is concentrated in a few individuals, the operation becomes fragile. Training must therefore go beyond basic use and include diagnostics, escalation logic, and safe recovery procedures.
Business evaluators should look for a realistic workforce plan tied to deployment phases. This should include role changes, training hours, support coverage, and expected time to operational maturity.
Cultural readiness matters too. If frontline teams view automation as disruptive, opaque, or imposed without process logic, adoption friction can delay benefits and increase error rates.
The strongest projects pair technology implementation with operating model adaptation. That includes ownership clarity, performance measurement, and practical support for daily decision-making on the shop floor.
A practical evaluation framework for decision-makers
To make better decisions, evaluators should use a structured framework rather than relying on vendor claims or generic ROI assumptions. A practical model can be organized around six questions.
First, what operational problem is the automation solving, and how critical is that problem to business performance? Second, what failure modes could interrupt value realization?
Third, how difficult is integration with current assets, software, and workflows? Fourth, what are the full lifecycle costs, including support, cybersecurity, upgrades, and training?
Fifth, how dependent will the factory become on one supplier, one protocol stack, or one set of specialists? Sixth, what evidence proves the system works in comparable industrial conditions?
These questions help separate strategic automation from technology enthusiasm. They also support clearer communication between procurement, operations, engineering, finance, and executive stakeholders.
For large industrial organizations, the best decisions usually come from cross-functional evaluation. Technical viability, commercial resilience, and operational fit should be tested together, not in isolation.
Conclusion: evaluate automation as a resilience investment, not just an efficiency project
Automation technology for factories can deliver major gains in output, consistency, labor optimization, and visibility. But for business evaluators, the real differentiator is not promised capability. It is risk-adjusted business fit.
The most important risks are rarely the most visible in sales materials. Integration gaps, downtime vulnerability, cybersecurity weakness, supplier lock-in, hidden lifecycle cost, and workforce readiness issues are where many projects stumble.
A sound evaluation process looks beyond technical appeal and asks whether the solution strengthens long-term resilience. If the answer is yes, automation can become a durable competitive asset rather than a fragile capital expense.
In today’s industrial environment, successful investment decisions depend on disciplined assessment, not automation optimism. The factories that benefit most are those that adopt with clarity, control, and a realistic understanding of risk.
Recommended News